Understanding the Critical Role of a VPN in Modern Digital Life
In an era where online risks are increasing, securing your private data has never been more vital. A VPN encrypts your online activity, ensuring that cybercriminals, network administrators, and external entities cannot track your browsing habits. Whether you’re accessing public Wi-Fi at a hotel or processing confidential files, a VPN acts as an digital shield against data breaches.
Individuals ignore the dangers of unsecured networks, exposing their credit card numbers, login credentials, and message histories. By redirecting your connection through encrypted servers, a 快连官网 masks your digital location and physical whereabouts, making it extremely difficult for tracking agencies to profile you.
Selecting the Ideal VPN for Your Device: A Comprehensive Comparison
Picking the right VPN tool depends on your specific needs and operating system. For Windows users, look for intuitive designs, quick performance, and advanced security. Mac users should prioritize flawless operation with iCloud services, while tech-savvy users may favor configurable options.
Smartphone users must opt for VPNs with compact software that limit battery drain and network load. Multi-device support is essential if you frequently switch between laptops, tablets, and devices. Always verify that your VPN works with latest protocols like OpenVPN for optimal performance.
Step-by-Step Guide to Installing a VPN on Microsoft’s OS
First, access the official VPN website using a trusted browser. Locate the download section and select the Windows-compatible edition. After acquiring the file, execute the installer and obey the on-screen prompts.
While configuring, customize preferences like auto-connect and encryption choice. Turn on the network lock feature to halt data leaks if the VPN disconnects. To conclude, sign in with your username and password and connect to a location of your choice.
Optimizing VPN Usage on Mac Systems
Mac systems provides integrated features for VPNs, but third-party apps often offer better functionality. Post-installation, drag the VPN program to your Applications folder. Launch the app and input your subscription details to activate the service.
Adjust settings such as security levels and geographical preferences. Turn on selective routing to channel certain programs through the 快连电脑版 while letting others to use your local network. For enhanced privacy, pair your VPN with security suites to prevent spyware and phishing attempts.
Securing Open-Source Platforms with a VPN
Tech enthusiasts often prefer VPNs that support command-line interfaces. Start with, updating your package manager to guarantee compatibility to the updated applications. Use terminal commands to deploy the VPN client, following documentation provided by your provider.
Configure system preferences to simplify VPN links during boot-up. Advanced users can embed firewall rules to block insecure connections. Periodically check reports to detect anomalies and upgrade your VPN application to resolve security gaps.
Protecting Smartphones with VPNs on Android and iOS
Mobile devices are frequent prey for cyberattacks due to their permanent internet access. Install your VPN software from the official marketplace to steer clear of fake apps. Launch the app, sign in, and pick a node nearby for faster speeds.
Activate options such as malware filtering to enhance your internet usage. Adjust the VPN to auto-connect when accessing open hotspots. For Apple mobile devotees, activate continuous protection in device settings to sustain encryption even if the app shuts down.
Advanced VPN Features to Elevate Your Privacy
Today’s services deliver get more info advanced features that surpass basic encryption. A emergency stop terminates all internet traffic if the VPN disconnects, blocking data exposure. Server chaining sends your connection through two or more locations, masking your digital trail to a greater extent.
Threat detection systems remove annoying pop-ups and prevent risky domains. Selective routing lets you select which apps use the VPN, optimizing speed and security. For organizations, static addresses and account control streamline encrypted communication.
Addressing Common Myths About VPNs
Despite their popularity, many users confuse how VPNs work. A common fallacy is that VPNs entirely anonymize your internet usage. While they mask your digital identity, tracking cookies can still reveal your details. Additionally, few VPNs practice zero-data retention rules, so investigating your provider’s practices is vital.
A further misconception is that VPNs severely limit network performance. While data scrambling introduces delay, premium services reduce this impact with high-speed networks. Lastly, free VPNs often undermine protection by monetizing user data or displaying tracking-based marketing.
Future-Proofing Your Online Presence with a VPN
As technology evolves, staying protected requires forward-thinking steps. Emerging trends like quantum computing could undermine current security protocols, making it crucial to opt for VPNs committed to upgrading their networks. Combining a VPN with supplementary measures like password managers and biometric checks establishes a multi-layered security strategy.
Governments worldwide are tightening digital rights regulations, and a VPN ensures you adhere with these standards. Whether you’re accessing media, engaging in eSports, or conducting business, a VPN remains an crucial tool for traversing the digital world securely.
 Danny Tamberelli Then & Now!
Danny Tamberelli Then & Now! Michael Bower Then & Now!
Michael Bower Then & Now! Loni Anderson Then & Now!
Loni Anderson Then & Now! Nancy McKeon Then & Now!
Nancy McKeon Then & Now!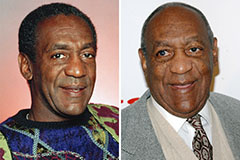 Bill Cosby Then & Now!
Bill Cosby Then & Now!